In July 2024, the world experienced one of the most significant IT outages in history. This massive disruption affected numerous industries, grounded flights, halted business operations, and caused widespread panic. The outage was triggered by a faulty software update from CrowdStrike, a leading cybersecurity firm, which led to system crashes and the infamous blue screen of death (BSOD) on countless Windows systems. This post explores how proper testing, adherence to the Software Development Life Cycle (SDLC), elimination of kernel access, strategic update deployment timing, intelligent automation with built-in rollback, and a phased rollout approach could have prevented this catastrophe.
The Sheer Magnitude of the Outage
The outage’s impact was felt across various sectors, including airlines, financial institutions, healthcare providers, and retail businesses. Flights were grounded, disrupting travel plans for millions. Banks experienced downtime, affecting transactions and online services. Hospitals struggled with patient management systems going offline, and retailers faced point-of-sale failures. The ripple effect was vast, with estimates suggesting hundreds of thousands of nodes were affected globally. The financial damage ran into millions of dollars, considering lost business, recovery costs, and reputational damage.
The Role of Proper Testing
Proper testing is the cornerstone of reliable software deployment. The logic error that led to the CrowdStrike outage was a null pointer issue in the memory-unsafe C++ language. This error could have been detected through rigorous testing phases, including unit, integration, system, and user acceptance testing.
Unit Testing
Unit testing involves verifying individual components of the software to ensure each part functions correctly. For CrowdStrike, thorough unit testing could have identified the null pointer issue early in the development cycle. Detecting such errors at this stage prevents them from propagating into more complex system interactions.
Integration Testing
Integration testing focuses on combining individual components and testing them as a group. Given the complex interactions within the CrowdStrike Falcon platform, comprehensive integration testing could have highlighted how the components interact under various conditions. This phase would have been crucial in identifying potential conflicts or errors arising from these interactions.
System Testing
System testing evaluates the entire system’s functionality as a whole. For a security platform like Falcon, this involves testing under realistic scenarios that mimic real-world usage. System testing would have exposed the logic error that led to the BSOD, allowing developers to address the issue before deployment.
User Acceptance Testing (UAT)
UAT ensures the software meets the end-users’ requirements and performs as expected in real-world scenarios. Engaging a subset of users in a controlled environment to test the update would have provided valuable feedback and revealed any issues that might not have been apparent in earlier testing stages.
Adhering to the Software Development Life Cycle (SDLC)
The SDLC provides a structured approach to software development, ensuring each phase is meticulously planned and executed. Adhering to the SDLC could have prevented the faulty update from reaching production systems.
Requirements Analysis
A thorough analysis of the requirements and potential impacts of the update would have highlighted the need for careful consideration of kernel-level changes. This phase involves understanding the software’s goals and constraints, and ensuring all stakeholder requirements are addressed.
Design
The design phase translates requirements into a blueprint for development. For CrowdStrike, this phase should have included detailed plans for handling kernel-level operations safely and strategies for mitigating risks associated with such deep system interactions.
Implementation
During implementation, developers write the code according to the design specifications. Following coding standards and best practices, particularly for memory management in C++, could have prevented the logic error.
Testing
As previously discussed, comprehensive testing at this stage is crucial. The SDLC emphasizes iterative testing and validation to ensure the software functions correctly and meets quality standards.
Deployment
Deployment should be approached cautiously, with strategies for minimizing impact and ensuring rollback capabilities. Adhering to the SDLC would have mandated a controlled and phased deployment, reducing the risk of widespread failure.
Maintenance
Post-deployment, continuous monitoring, and maintenance ensure the software remains functional and secure. Rapid identification and resolution of any issues that arise during this phase are critical to maintaining system integrity.
Eliminating Kernel Access
Kernel access allows software to interact with the core of the operating system, providing powerful capabilities but also posing significant risks. Microsoft has repeatedly declined to block kernel access, citing the need for certain applications to perform low-level operations. However, eliminating or restricting kernel access could have prevented the CrowdStrike outage.
Risks of Kernel Access
Kernel access can lead to severe system instability if not managed correctly. A single error can cause widespread crashes, as seen in the CrowdStrike incident. Restricting kernel access minimizes these risks, ensuring only trusted and thoroughly tested code interacts with the operating system core.
Alternatives to Kernel Access
Modern security solutions can achieve high levels of protection without kernel access. Techniques such as user-mode hooks and virtualization-based security offer robust alternatives. Encouraging the development and adoption of such methods can enhance security without compromising system stability.
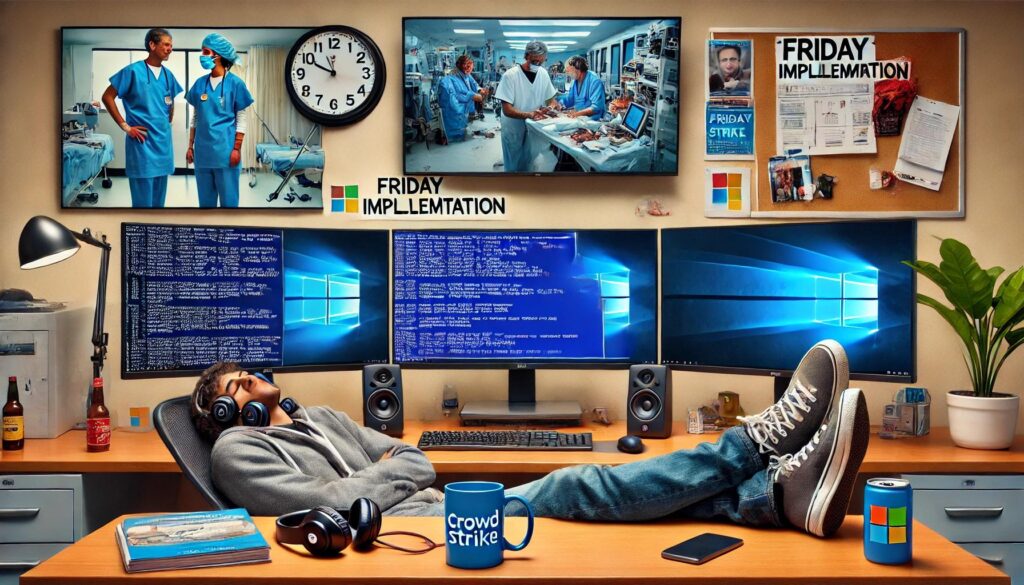
Strategic Timing for Updates
Deploying updates earlier in the week ensures more IT staff are available to respond to any issues. The CrowdStrike update was deployed on a Friday, a time when many offices are winding down for the weekend, and IT resources are limited.
Risks of Friday Deployments
Deploying updates late in the week increases the risk of extended downtime, as fewer IT staff are available to address problems promptly. This delay can exacerbate the impact of any issues that arise, leading to prolonged disruptions.
Best Practices for Deployment Timing
Scheduling updates for early in the week, preferably on Monday or Tuesday, ensures maximum IT support availability. This approach allows for swift identification and resolution of issues, minimizing downtime and reducing the impact on business operations.
Intelligent Automation with Built-In Rollback
Intelligent automation can streamline the update process, but it must include robust rollback mechanisms to handle unforeseen issues. The CrowdStrike update lacked such capabilities, leading to widespread system failures that required manual intervention.
Automated Deployment
Automated deployment tools can ensure consistent and efficient update rollouts. These tools can handle complex deployment tasks, reducing the likelihood of human error and ensuring updates are applied correctly across all systems.
Rollback Mechanisms
Built-in rollback mechanisms allow updates to be quickly reversed in case of issues. These mechanisms can restore systems to a previously stable state, minimizing downtime and preventing widespread disruptions. Implementing automated rollback procedures ensures swift recovery from failed updates.
Phased Rollout Approach
A phased rollout approach distributes the update to a small subset of users first, allowing for controlled testing and feedback before broader deployment. This strategy could have prevented the CrowdStrike outage by catching issues early.
Pilot Testing
Pilot testing involves deploying the update to a limited group of users or systems. This controlled environment allows for real-world testing without risking widespread disruption. Feedback from pilot testing can reveal unforeseen issues and provide valuable insights for further refinement.
Gradual Deployment
Gradual deployment extends the update to additional users or systems in phases. This approach ensures any issues that arise can be addressed before affecting a larger audience. It also allows IT teams to manage the rollout more effectively, ensuring adequate support is available at each stage.
Monitoring and Feedback
Continuous monitoring and feedback during the phased rollout ensure any issues are promptly identified and addressed. This iterative process allows for continuous improvement, enhancing the reliability and stability of the update.
Conclusion: Lessons Learned and Path Forward
The Microsoft-CrowdStrike Outage of July 2024 highlights the critical need for robust testing, adherence to the SDLC, restricted kernel access, strategic deployment timing, intelligent automation, and phased rollouts. Each of these components plays a vital role in ensuring software updates are reliable, secure, and minimally disruptive.
By implementing comprehensive testing and adhering to the SDLC, developers can identify and address potential issues before they reach production systems. Restricting kernel access minimizes the risk of severe system failures, while strategic timing ensures adequate IT support is available to handle any issues that arise. Intelligent automation with built-in rollback mechanisms provides a safety net for unforeseen problems, and a phased rollout approach allows for controlled testing and feedback.
The lessons learned from this incident must drive changes in how we approach software development and deployment. Businesses and IT professionals must prioritize these best practices to prevent future outages and ensure the stability and security of their systems. Only through a concerted effort to improve our processes and technologies can we avoid repeating the mistakes of the past and build a more resilient and reliable IT infrastructure for the future.

Nabeil Sarhan, MBA, is a dynamic technology delivery manager with over 15 years of experience in tech, cybersecurity, and computing scalability. He excels in leading diverse teams and delivering enterprise-class systems across industries such as healthcare, finance, and retail. Nabeil’s passion for solution design, systems architecture, and performance optimization makes him a sought-after consultant. He holds degrees from Harvard, MIT, and Bryant University. Connect with Nabeil on LinkedIn or Twitter